5 ways that Celigo integrator.io ensures data security for cloud integrations
Learn how Celigo safeguards your integrations with robust security measures

At Celigo, we prioritize data security on the Celigo Platform by using a variety of strategies to prevent data breaches. While the most commonly integrated SaaS applications often have extensive security systems in place to protect sensitive data within the apps themselves, transferring data from one system to another opens up a host of security vulnerabilities. integrator.io helps you mitigate the following risks:
- External connections, API endpoints, and internal connections can be vulnerable without HTTPS & TLS 1.2. FTP sites and connections can be vulnerable without SFTP or FTPS. You should never use unsecured FTP. While integrator.io allows you to connect to unsecure endpoints, we highly recommend that you protect the endpoints you are connecting to with HTTPS and TLS1.2. All internal connections used by Celigo are protected with HTTPS and TLS 1.2.
- Unencrypted data temporarily at rest could be at risk in other systems, but integrator.io always encrypts data at rest.
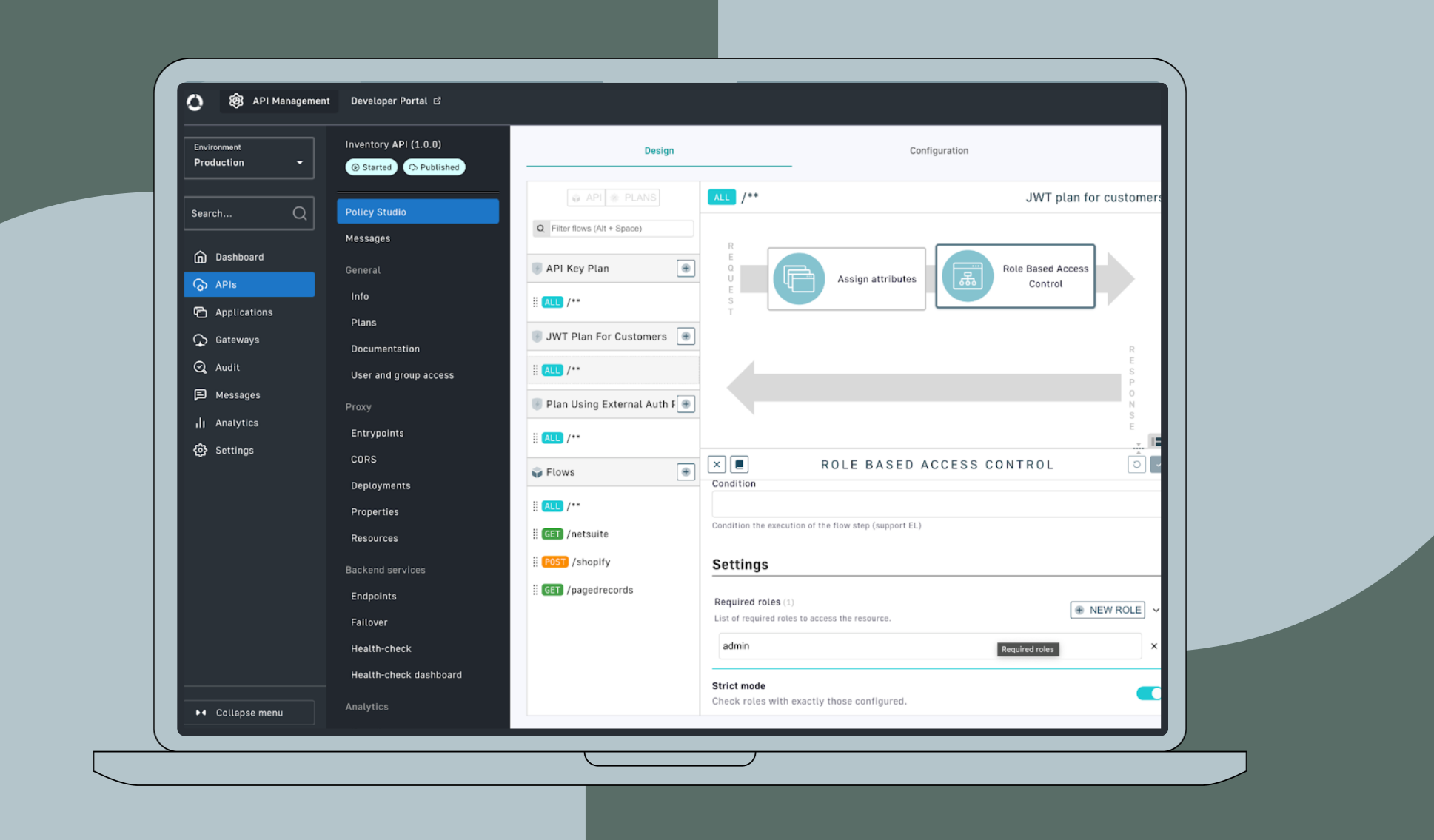
- Organizational risk can jeopardize your data, so you should only grant environmental access to minimal trusted staff and have well-configured notification and user-audit systems in place. integrator.io has several tools that allow you to securely manage user access. For example, the diagram below showcases a customer organization managing their user accounts and utilizing single sign-on authentication with integrator.io.

- Physical and environmental anomalies can put your data at risk. Our website uses the security features available via Amazon Web Services (AWS). AWS has extremely tight physical and environmental security.
We also make it easy for you to reduce risks with the following five cloud integration security features to ensure that sensitive information is never compromised during data migration between systems.
Key takeaways: Ensuring data security
- Celigo’s iPaaS temporarily stores in-process data in Amazon S3 for up to 30 days to ensure data integrity, enable error recovery, and facilitate retries, but automatically deletes it upon successful integration.
- Celigo stores core application data in a highly available MongoDB cluster, with multiple daily backups via MongoDB Atlas, while encrypting sensitive credentials using AES 256 or pbkdf2, with decryption keys securely stored on a separate server.
- Celigo ensures robust data security by conducting annual audits, SOC 2 Type 2 assessments, penetration testing, and vulnerability testing while complying with industry standards such as GDPR, CCPA, HIPAA, and FERPA.
- Celigo’s platform allows organizations to customize user access with role-based permissions, enabling account owners and administrators to assign, transfer, promote, or restrict user roles as needed.
- Celigo supports Single Sign-On (SSO) with OpenID Connect (OIDC), providing centralized access control, enhancing security, reducing password fatigue, and improving organizational efficiency.
1. integrator.io doesn’t persistently store processed data
First, think of integration as a pipeline of data traveling between endpoints. The in-process data that you are integrating may be temporarily stored in Amazon S3. This data is securely stored for up to 30 days to preserve data integrity while in transit or to facilitate error recovery and retry capabilities when applicable from an authenticated page within integrator.io, but is deleted on successful integration.
All in-process data is deleted after completing the integration. However, since integrator.io allows you to build integrations between nearly any two systems that have a compatible API, Celigo has a list of considerations for security experts to take into account when protecting data in transit.
2. Credential encryption and process flow data storage
A highly-available MongoDB cluster stores all Celigo integrator.io core application data (credentials, integration flow components, and other customer-specific data), and MongoDB Atlas generates full backups of this data multiple times each day. The sensitive credential data and all other data used to access the different applications and systems you’re integrating is always encrypted via AES 256 or pbkdf2 before being persisted to the database.
This data is never viewable in plain text by anyone. Instead, the encryption keys used to decrypt credential data are always kept on a separately secured server other than the server that stores the encrypted data at rest.
3. Data security, information privacy, and PII standards
We perform annual audits of our platform and general company management practices to verify that they meet and exceed all data security requirements. These requirements include the following:
- Trust services criteria relevant to Security and Availability (applicable trust services criteria) set forth in TSP section 100
- 2017 Trust Services Criteria for Security, Availability, Processing Integrity, Confidentiality, and Privacy (AICPA, Trust Services Criteria)
- Celigo also has the resulting SOC 2 Type 2 report available under NDA.
We also perform annual Pen Testing and Quarterly Vulnerability testing, and a summary of the Pen testing is available under NDA. In addition, Celigo always processes data in accordance with the following data security regulations:
- EU/UK GDPR
- CCPA
- HIPAA
- FERPA
4. User account management
You can customize user accounts for people within your organization who access integrator.io. Account owners have full permission to perform all possible actions in an account, and can transfer their account ownership to a different user if necessary.
However, you can assign administrator, manage, or monitor permissions to any user who accepts your invitation. Both account owners and administrators can promote or demote other users as needed. See Manage account and integration permissions for all information related to user permissions.
5. Single sign-on (SSO) authentication security
Lastly, you can set up SSO authentication for all users who access integrator.io, so you can have centralized control of who has access to the platform. SSO also reduces password fatigue because team members only need to remember a single username/password that grants them access to multiple systems. SSO authentication boosts security, lowers IT help desk burdens, and increases organizational efficiency.
The platform supports any SSO provider that offers OpenID Connect (OIDC) authentication. For more information, see Enable single sign-on (SSO).
You can rest assured that your integration data is safe by using these built-in security features and by followingthe recommended security configurations in our knowledge base. Feel free to contact a Celigo representative if you have any questions regarding the data security strategies available through integrator.io.
Integration Insights
Expand your knowledge on all things integration and automation. Discover expert guidance, tips, and best practices with these resources.